Passage #207: 17 July 2013
Sentinel Education
Vigilance has always been an important part of security. In order to respond to threats, one must first identify them. One must keep an eye open.
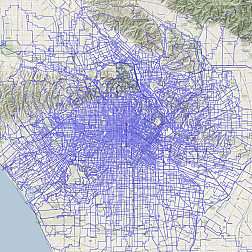
These days, this generally means an electronic eye peering down into the data abyss. They are scanning our communications, of course, but also following the information footprints we leave in the sand. (Silicon comes from sand, right? So surely that data abyss is lousy with sand in which footprints can be left.) They go way overboard with this, sweeping the virtual dragnet over basically everyone and everything, looking for patterns. Search histories, social network connections, transaction records -- they're probably always there, looking over our shoulders, quietly watching. It's just software somewhere in a plastic box, churning away; omniscience is only questionably more effective but it is certainly more efficient. Setting up reasonable limits is difficult.
This wasn't always the way. Following all the information in an analog world meant following all the people, taping all the phone calls. They couldn't do that. They would've ended up with a Borgesian map, reduplicating the world. So they had to focus on the big targets. This meant tracking movements and communications selectively, with some degree of precision. But it also meant setting up on the top of a tall hill and watching out for literally big targets hurling towards us through the sky. Quaint!
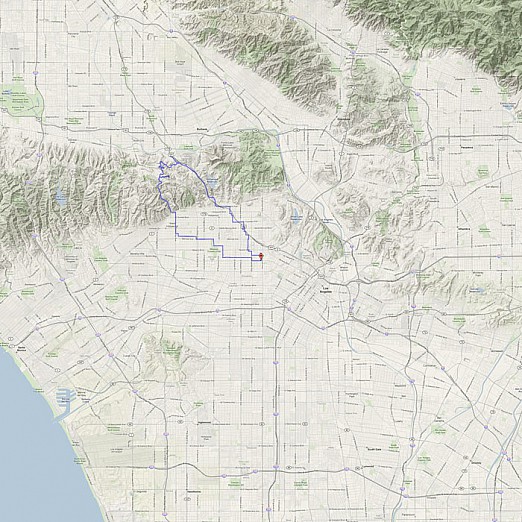
This week we make some decidedly non-virtual movements up some decidedly non-virtual hills and see what we can learn.